In this post, we will discuss how to send an email alert when a user adds/deletes objects in a s3 bucket. We will use a case scenario to describe the process. The entire solution will be done using AWS console and email with Simple Notification Service (SNS). Other possible SNS solutions not discussed here includes SMS, Amazon SQS, AWS Lambda etc.
Malpaso is a Hollywood production company, founded by Clint Eastwood. The company has setup multiple s3 buckets holding different movie details, screenplays and other footage. But there is a s3 bucket (malpaso-finance-s3-bucket) containing financial details that should be only accessible by the Chief Executive Officer (Clint Eastwood) and Chief Financial Officer (Tom Cruise). Other executive producers within the company such as Mel Gibson should not have access to that s3 bucket. As a Solution Architect, you have been asked to setup this process and test the solution.
The step by step process is shown below.
- Step 1 – Setup IAM users without any permission, then create groups and add permissions to it and then add relevant users to the appropriate groups
- Step-2 – Create the s3 bucket [malpaso-finance-s3-bucket]
- Step 3 – Create a SNS topic and email subscription
- Step-4 – Create s3 bucket event notification and configure with the SNS topic
- Step-5 – Update SNS Access Policy and configure with the s3 bucket ARN
- Step-5 – Update bucket policy for the s3 bucket [malpaso-finance-s3-bucket] with the username who will be denied access
Step-1: Setup IAM users
Since only Clint Eastwood and Tom Cruise should have access to the [malpaso-finance-s3-bucket] while the other staff of the company such as Mel Gibson should not, the best way to set this up is to setup the IAM user accounts without permission and then add the users to groups with relevant permissions. Hence, a “management” group is created for Clint Eastwood and Tom Cruise which has Administrator Access to all of AWS services while a “staff” group is created for Mel Gibson which has FullAccess permissions to all s3 buckets.
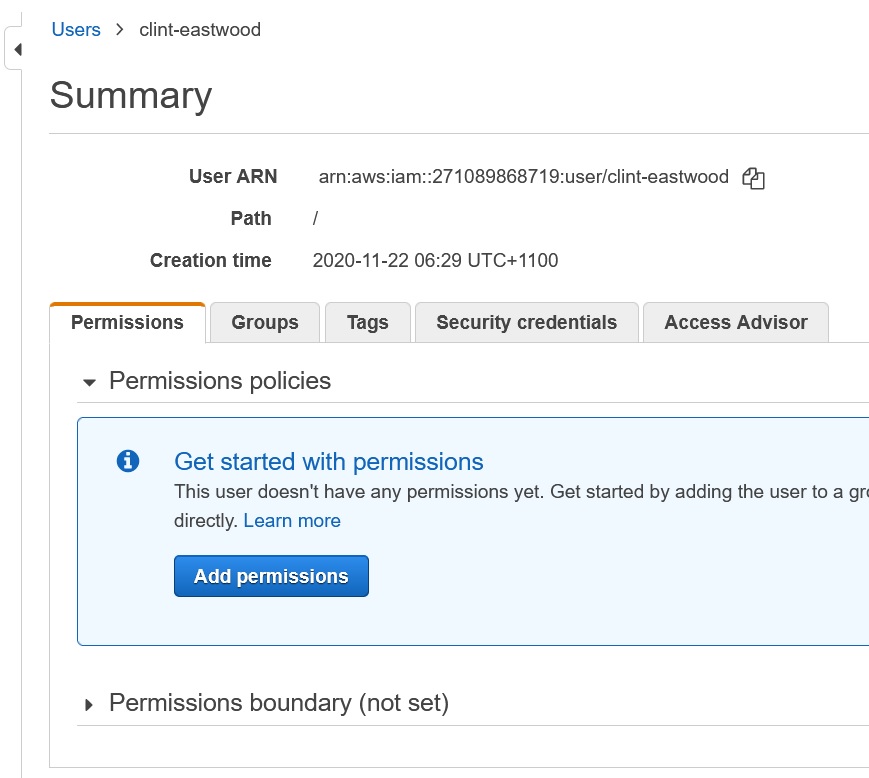
As can be seen below, “clint-eastwood” IAM user account is created with no permissions.
Similarly “tom-cruise” and “mel-gibson” IAM users are also created.
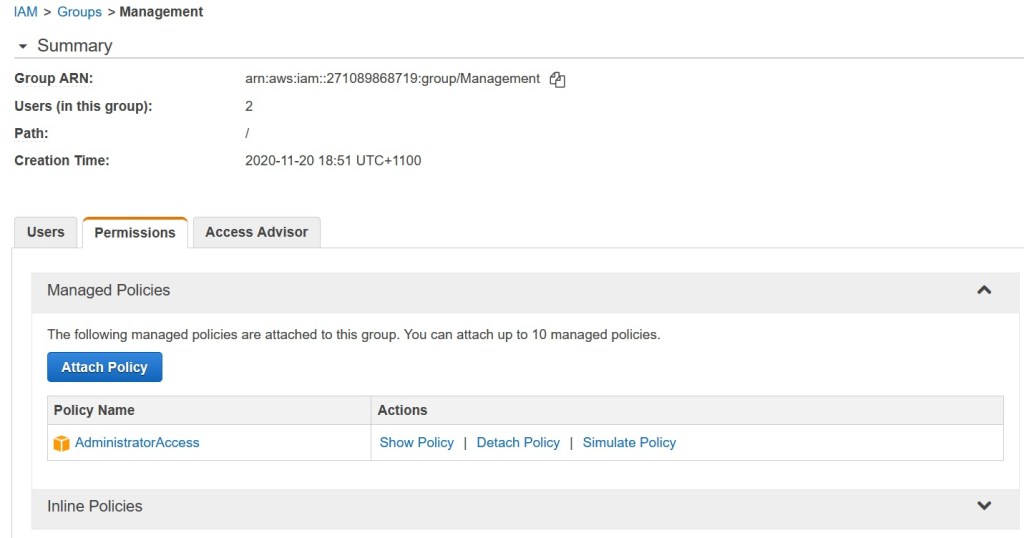
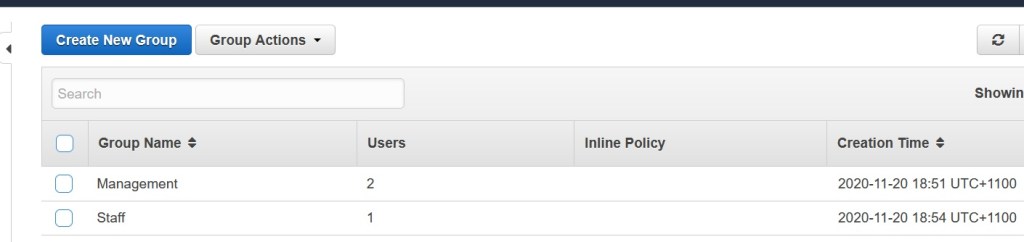
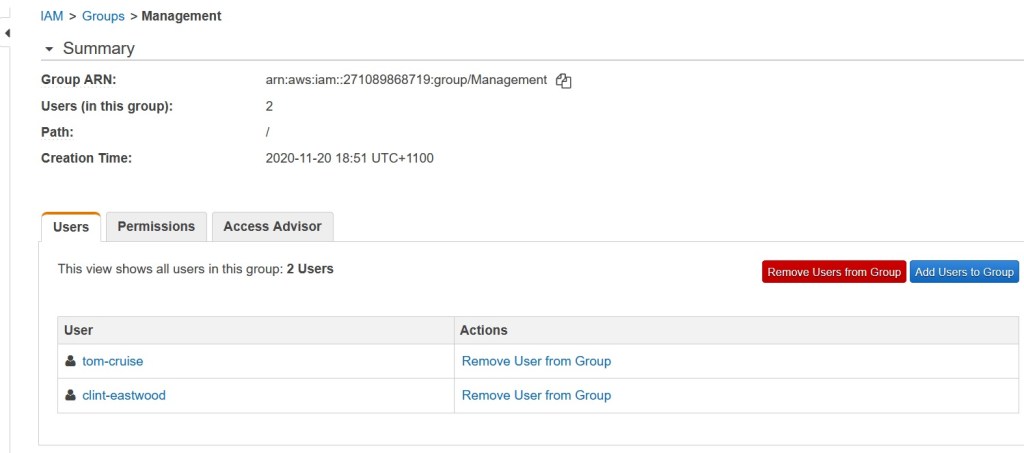
Now, create a group called “management” and attach [AdministratorAccess] permission to this group.
Similarly, create a group called “staff” and attach [AmazonS3FullAccess] permission to it.
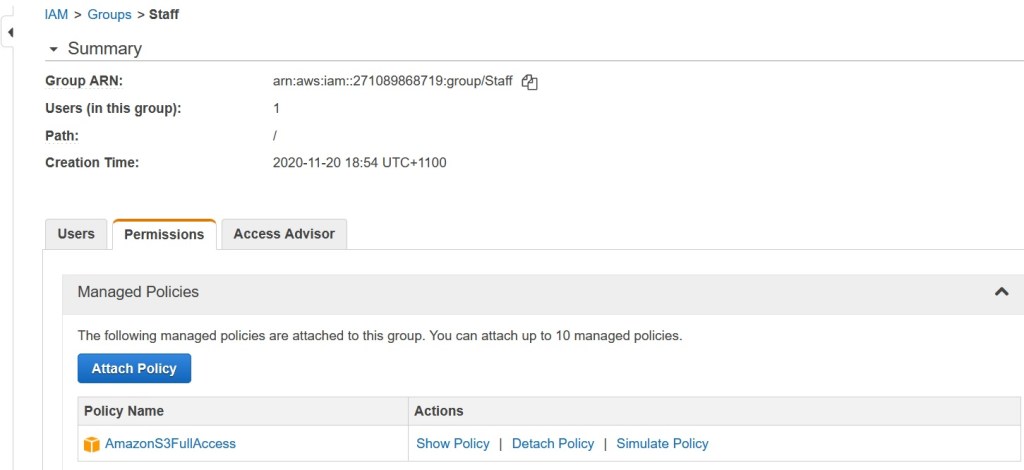
Now, add “clint-eastwood” and “tom-cruise” IAM users to “management” group while add “mel-gibson” IAM user to “staff” group. These users then inherit the permissions from their corresponding groups.

But Why? Why did we do it this way?
We did it this way because it is an easy way to manage groups and relevant permissions. Say for example, we have two groups: developer and tester. If we have 50 developers and 30 testers then it is much easier to add IAM users to developer group where each user will inherit the same permission than edit each one of the 50 IAM users and change their permissions. If any developer moves to the tester group, all you have to do is remove that IAM user from developer group and add them to tester group and you are done! It is that ease of maintenance why IAM users have been setup this way in this post.
Step-2: Create a S3 Bucket
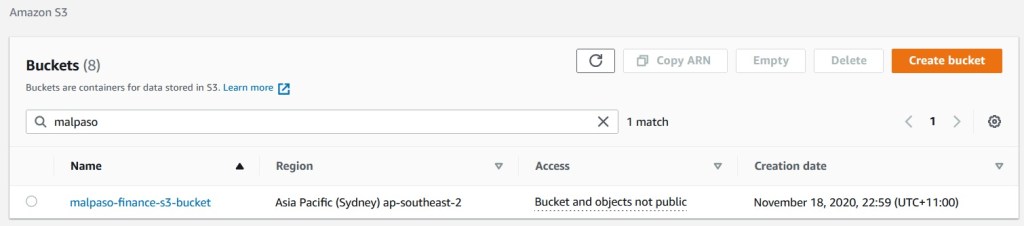
Now create a s3 bucket called “malpaso-finance-s3-bucket”. The name has to be globally unique. There is not much to this process and you should already know how to create a s3 bucket. At this point, it is an empty bucket with no other changes configured. Note that All Public Access is blocked as the objects in this s3 bucket should not be made public.
Step-3: Create Simple Notification Service (SNS) Topic and Email Subscription
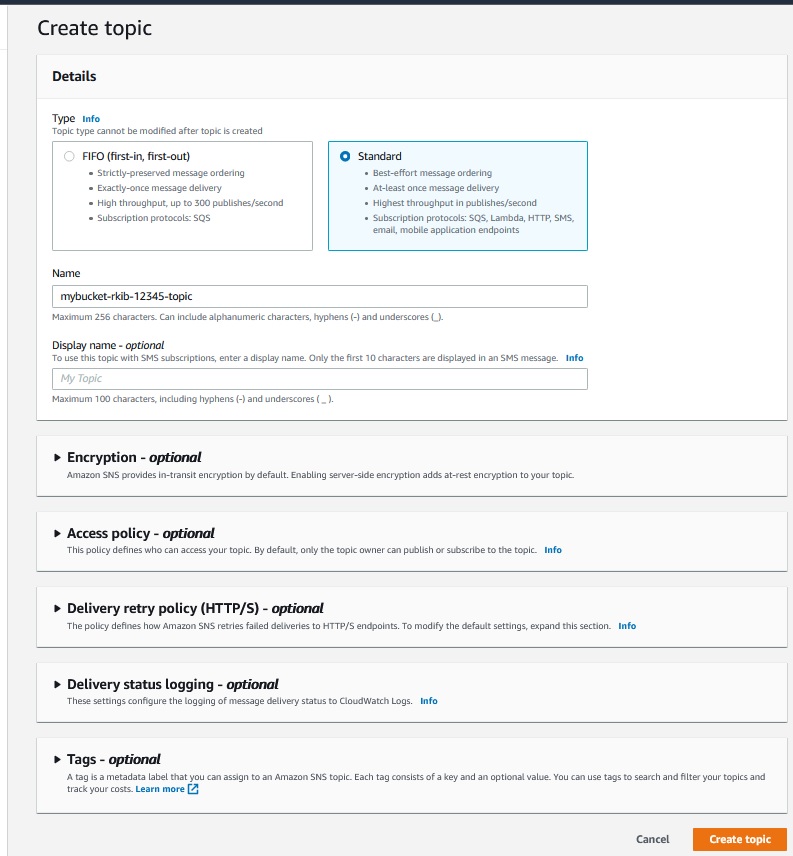
It is now time to setup email notification. So we need to create a SNS topic first.
Except for the name, leave everything as default when creating the topic [type as Standard].
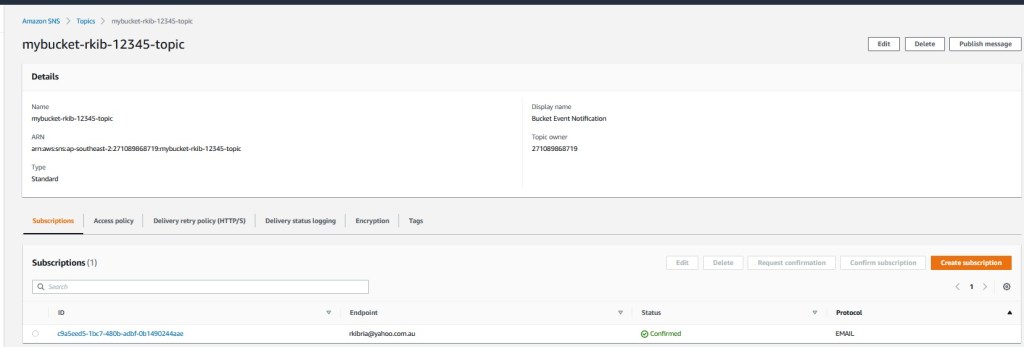
Open the topic and create subscription. Select “Email” as the subscription protocol and enter your email address under end point.
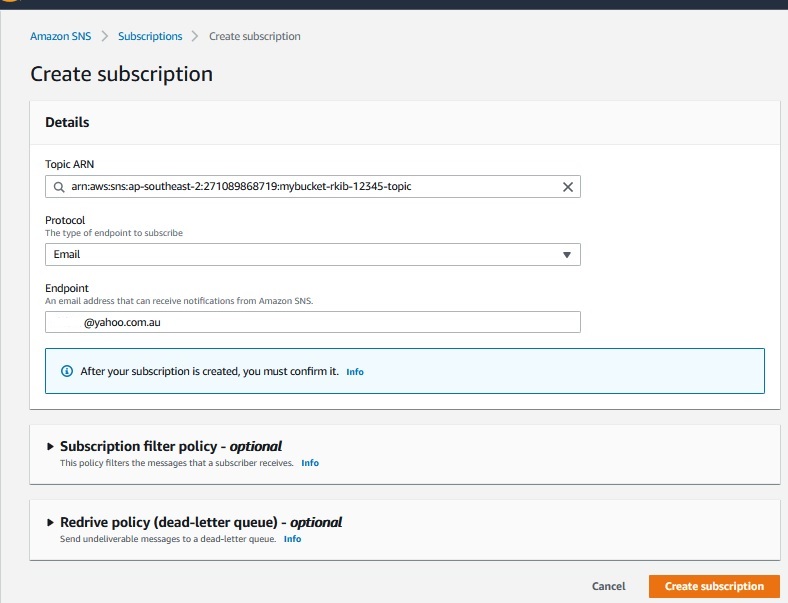
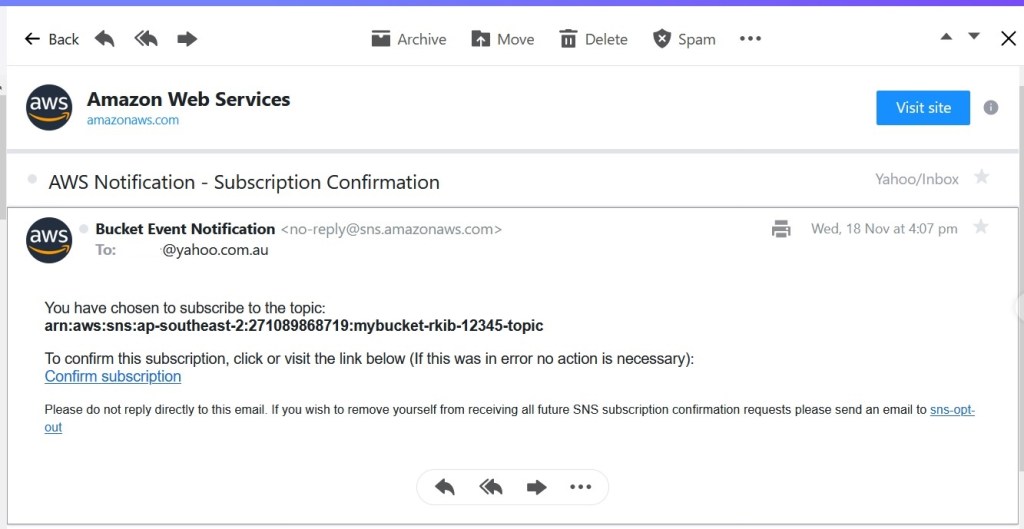
A confirmation email will be sent to that email address. Until that email is confirmed, subscription will remain in “pending” state.
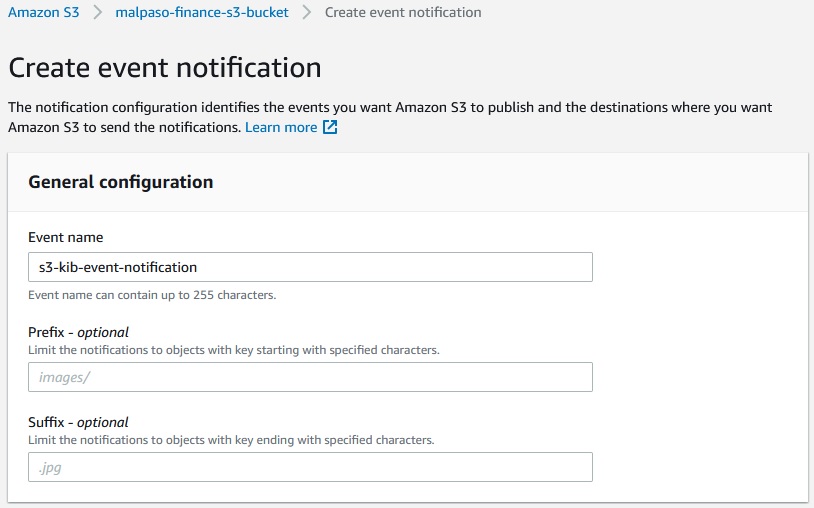
Step-4: Create S3 Bucket Event Notification
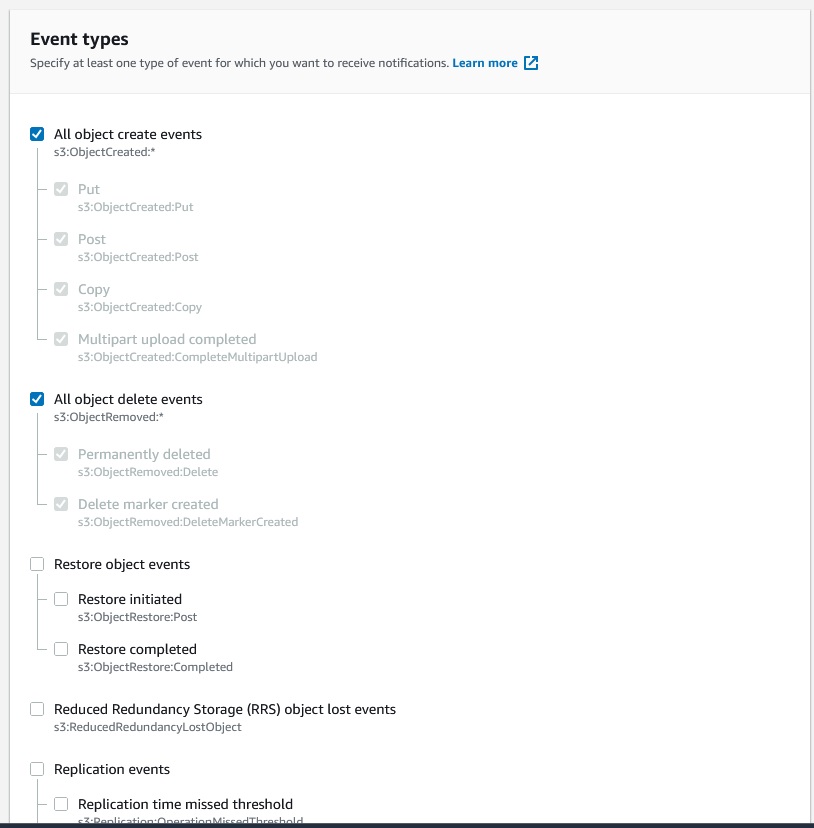
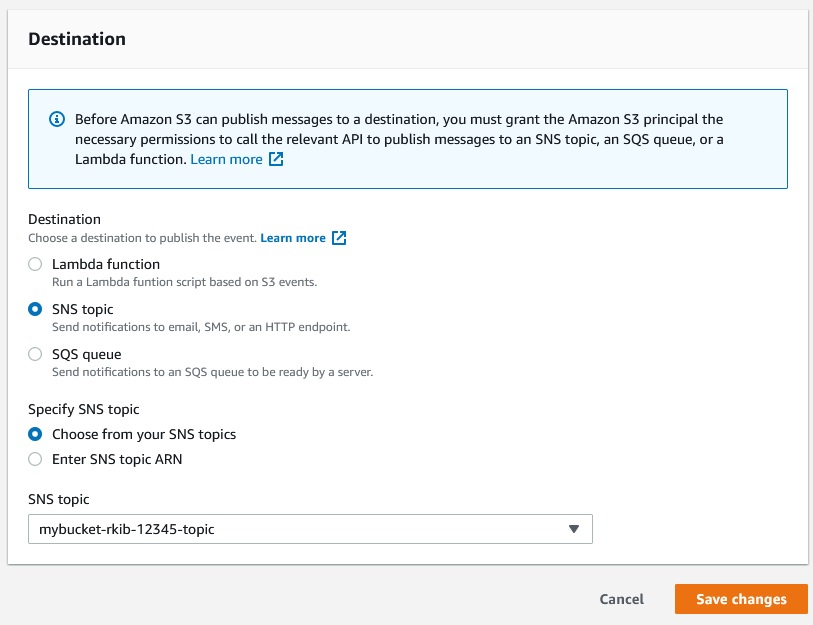
On AWS console, go to s3 services and open [malpaso-finance-s3-bucket] > Properties and scroll down to Event Notification section. Now create event notification for All object create and All objects delete events as below. Under destination section, select the SNS topic created in step-3. Save the changes.
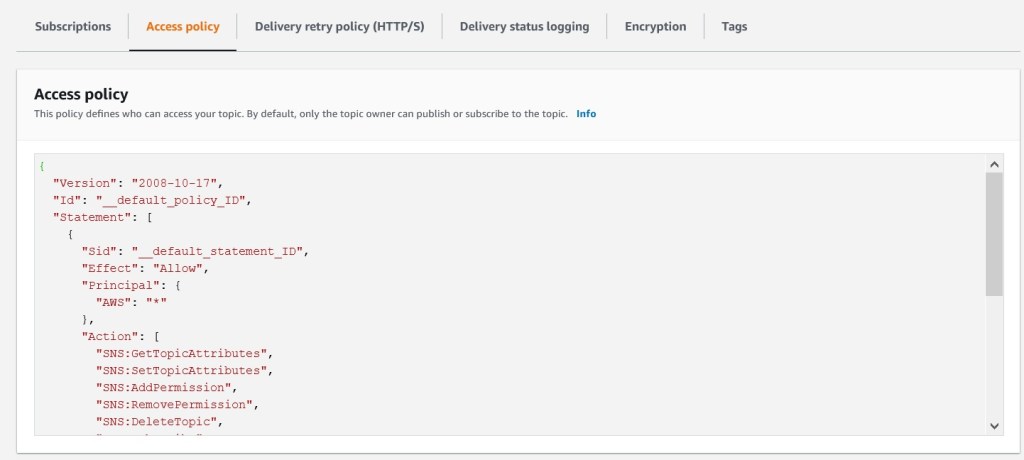
Step-5: Update SNS Access Policy
Now open the SNS topic and open Access Policy. Then update the last few lines to below JSON code [highlighted below]. As can be seen, “Condition” is set to “ArnEquals” and ARN is matched to s3 bucket ARN: [arn:aws:s3:::malpaso-finance-s3-bucket].

Step-6 : Update Bucket Policy
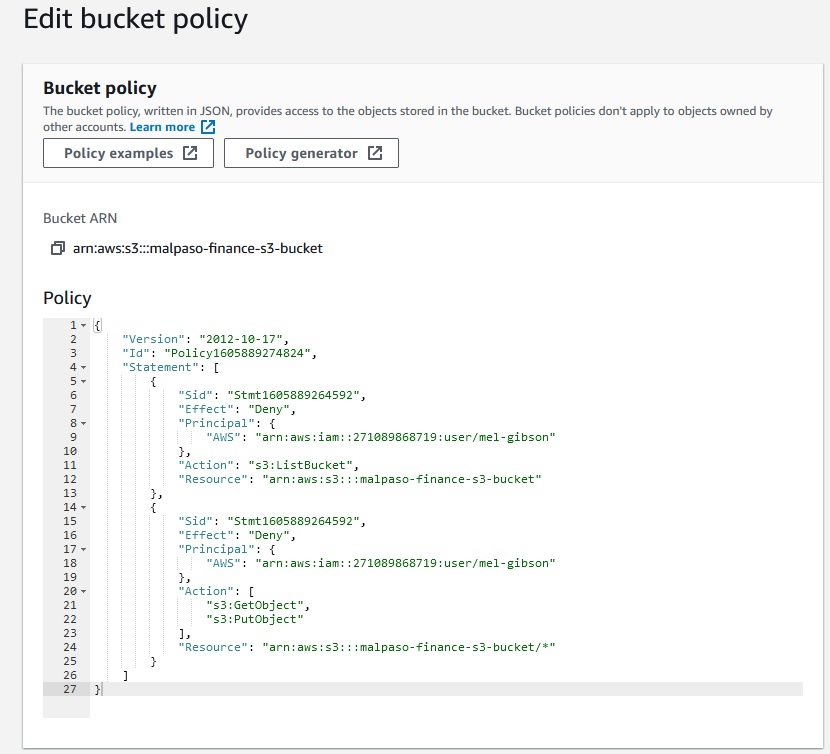
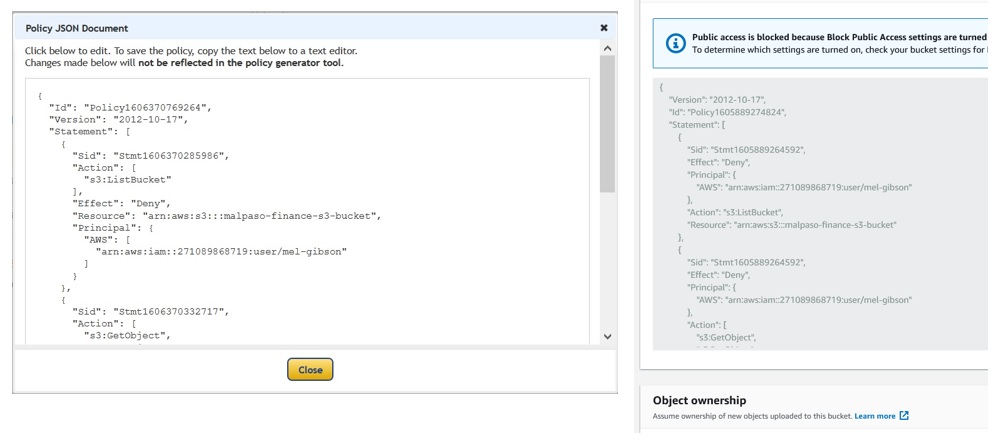
Now that the solution is in place, it is time to configure the s3 bucket to deny access to “mel-gibson”. For this, we need to configure the bucket policy. Open the s3 bucket and under permissions, scroll down to Bucket policy section of the UI. Use the below JSON policy and save the changes.
So how did we generate the JSON policy? To do this, click the Policy Generator button (within the bucket policy section) to open the Policy Generator UI. You don’t need detailed JSON knowledge to generate the policy. In the below UI, the fields are populated as per below guidelines.
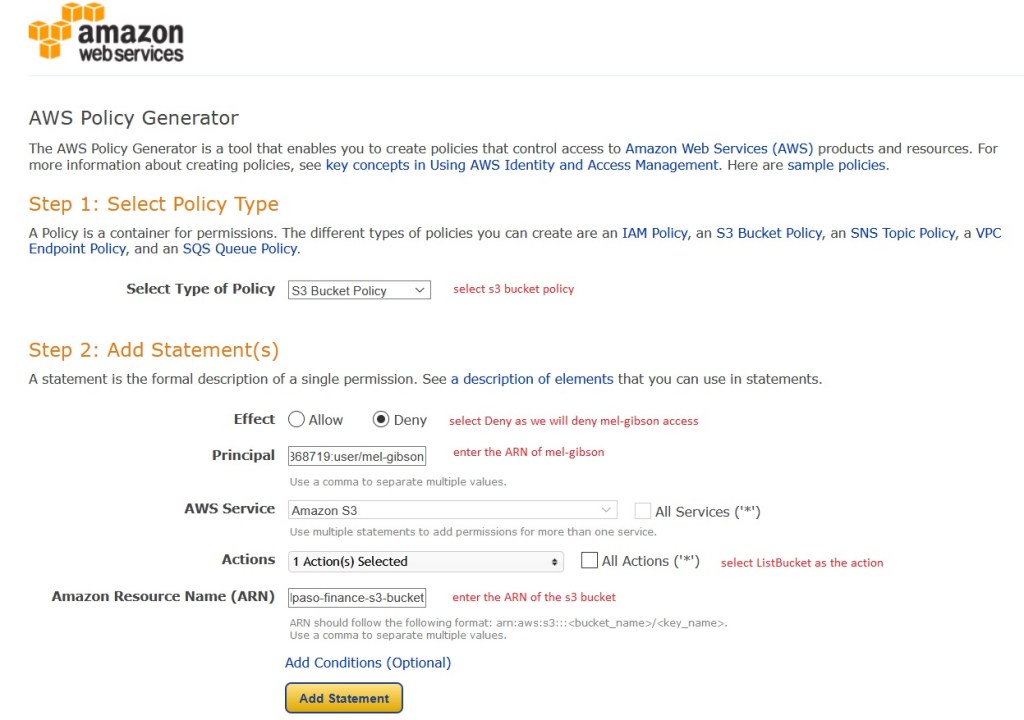
Click Add Statement to generate the required statement. Repeat the process with below requirements so that the following two statements are generated.
- Statement 1 – here mel-gibson is denied access to perform the ListBucket action on the s3 bucket. This means that when mel-gibson opens the s3 bucket [he is still able to see the bucket among all other buckets], he will not be able to see any content of the s3 bucket as access is denied. Hence the s3 bucket ARN is unchanged here.
- Statement 2 – here mel-gibson is denied access to perform GetObject (means read content of the bucket) and PutObject (means add new object to the bucket) on the s3 bucket. This means that when mel-gibson tries to upload any object, that action will fail.

Click Generate Policy which will generate the below policy. Copy and paste this entire policy in the s3 bucket policy UI.
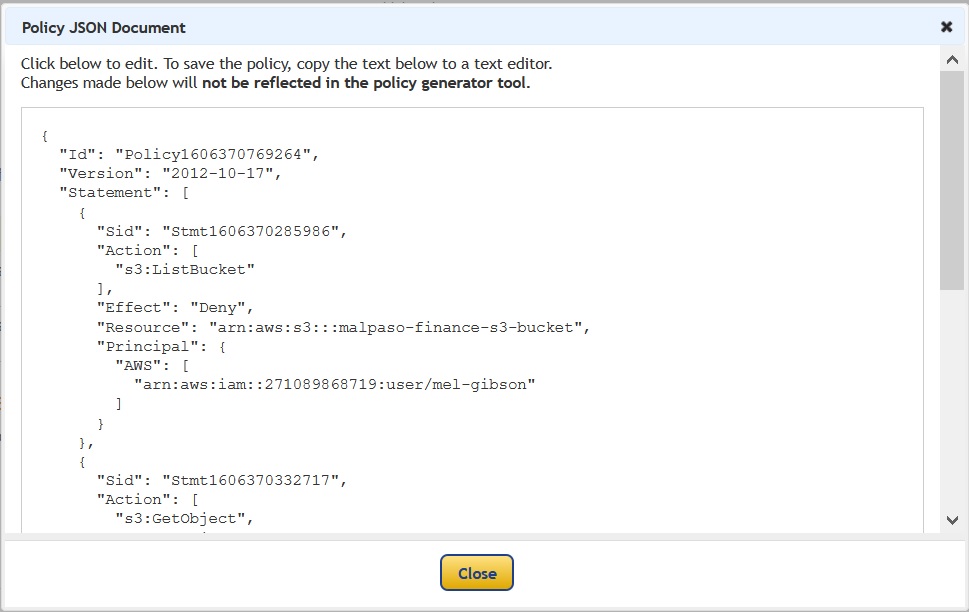
We see that the policies are identical, albeit a little bit re-arranged.
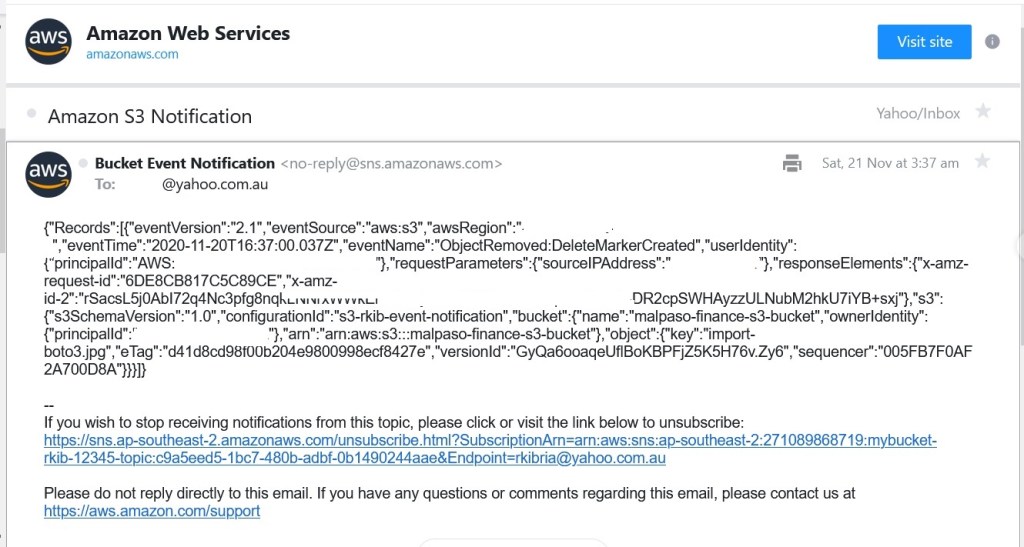
So now whenever clint-eastwood or tom-cruise adds or deletes one or more objects from this s3 bucket, an email alert will be sent to clint-eastwood as his email has been configured in the SNS email subscription.
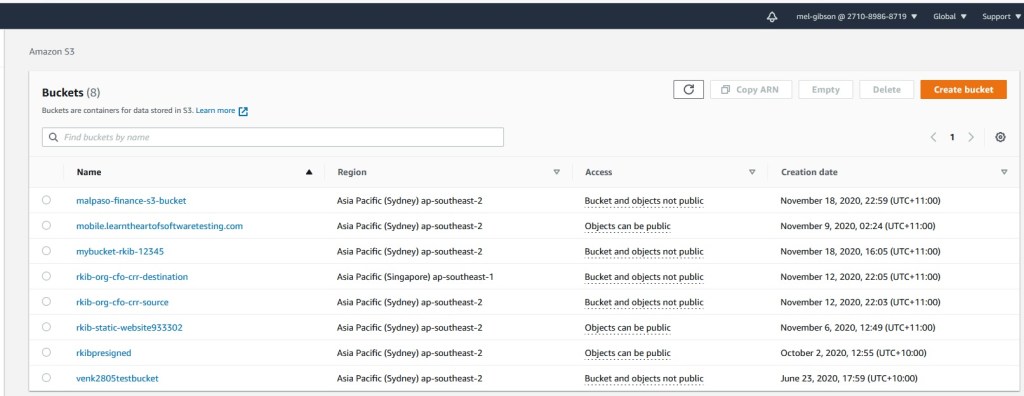
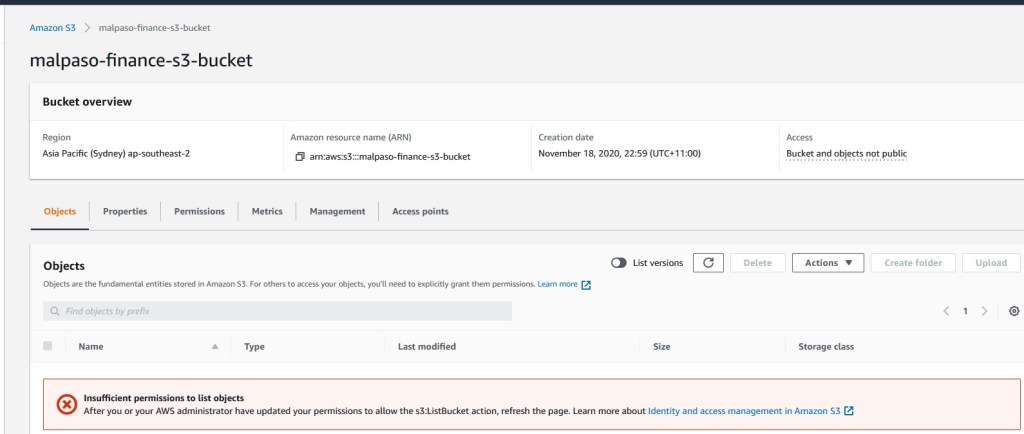
When mel-gibson tries to open the [malpaso-finance-s3-bucket] s3 bucket to see the financials of the “Gran Torino” movie, although he can see all s3 buckets created for the Malpaso company, he cannot see the content of the malpaso-finance-s3-bucket because he does not have sufficient permission to list objects in the bucket. Mel is obviously not happy, but that is just Hollywood for you.
So how will you test this solution? Consider the below test scenarios:
- Remove the JSON code that denies ListObject action for mel-gibson. What can Mel see when he opens the [malpaso-finance-s3-bucket]?
- How would you prevent mel-gibson from even seeing the [malpaso-finance-s3-bucket] s3 bucket in the entire s3 bucket list?
- How would you only trigger email alerts when tom-cruise adds or deletes objects in the [malpaso-finance-s3-bucket] but no alert is sent when clint-eastwood does the same?
- If more users need to be denied access to [malpaso-finance-s3-bucket], how would the bucket policy look like? What JSON code needs to be updated?
